Show Focus Points
2019 update released! Check out download page for details
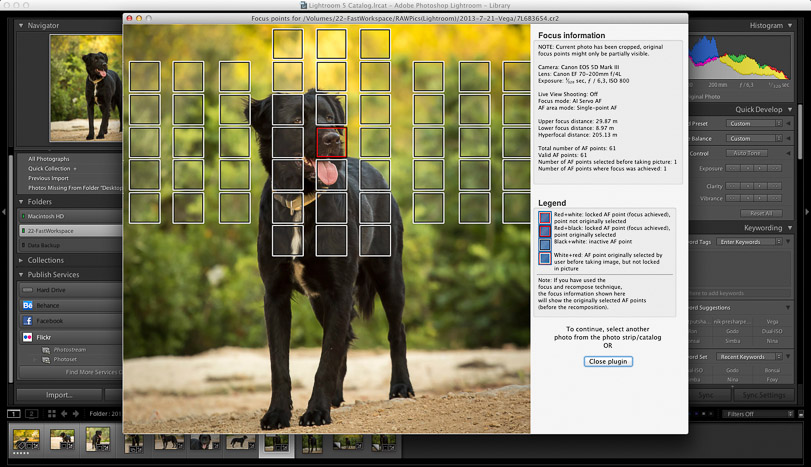
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
Show Focus Points
2019 update released! Check out download page for details
Show Focus Points is a plugin for Adobe Lightroom. It shows you which focus points were selected by your camera when the photo was taken.
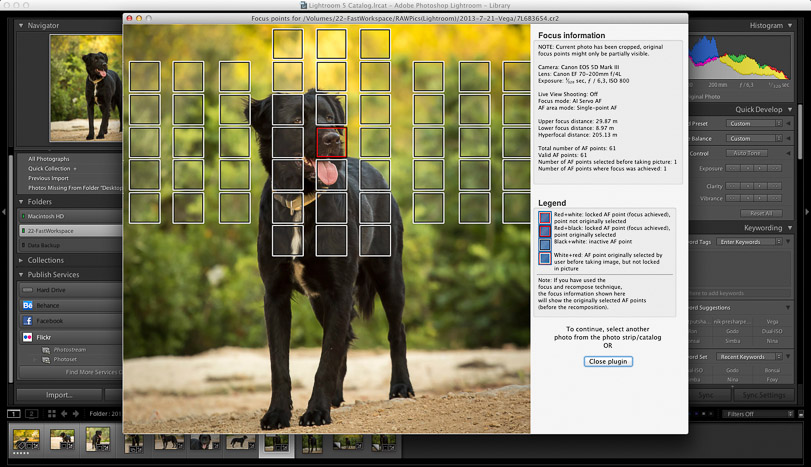
Show Focus Points is a plugin for Adobe Lightroom which shows you which of your camera's focus points were used when you took a picture.
Below find some screenshots of the plugin in action.
Click on the images to enlarge them.
Download Mac-only version (6.6 MB)
Download Windows-only version (14 MB)
Download version containing both Mac+Windows versions (20 MB)
Why? Because six months ago, an intern had accidentally promoted a test beacon file to production, then deleted it—but never purged it from Tripwire’s historical baseline. When the RAM error produced the same hash by pure coincidence, Tripwire thought someone had maliciously swapped in the old test file.
One night, her phone buzzed at 3:00 AM. It wasn't the usual “transfer complete” alert. It was . tripwire filecatalyst
She cross-referenced the timestamps. FileCatalyst said: "File delivered intact. SHA-256: 7A8F... valid." Tripwire said: "File altered at 02:14:33. New hash matches 'test_pattern_old.dat'." One night, her phone buzzed at 3:00 AM
The alert was cryptic: /data/incoming/seismic_scan_04.bin had changed. But not just changed—its hash signature had flipped to a value that matched a known beacon from a test environment decommissioned six months ago. She cross-referenced the timestamps
Then she saw it. The Svalbard station’s ingest server had a silent RAM error—a single bit flip in a memory module used by the post-processing script. When the script ran 14 minutes after the transfer, it corrupted the file on disk. But here was the kicker: the corrupted file’s hash accidentally matched an old test signature Tripwire still had in its baseline.
Marta’s heart raced. She pulled up the FileCatalyst transfer logs. The file had arrived on time. But Tripwire showed that 14 minutes after FileCatalyst reported a successful checksum, the file had mysteriously been overwritten.
Marta was the lead security engineer for Arctic Helix , a joint polar research initiative. Every six hours, a 200GB seismic dataset from a remote ice station in Svalbard needed to be shipped to a supercomputer in Oslo. They used for this—it was the only thing that could push data that heavy across a shaky satellite link without failing.
Why? Because six months ago, an intern had accidentally promoted a test beacon file to production, then deleted it—but never purged it from Tripwire’s historical baseline. When the RAM error produced the same hash by pure coincidence, Tripwire thought someone had maliciously swapped in the old test file.
One night, her phone buzzed at 3:00 AM. It wasn't the usual “transfer complete” alert. It was .
She cross-referenced the timestamps. FileCatalyst said: "File delivered intact. SHA-256: 7A8F... valid." Tripwire said: "File altered at 02:14:33. New hash matches 'test_pattern_old.dat'."
The alert was cryptic: /data/incoming/seismic_scan_04.bin had changed. But not just changed—its hash signature had flipped to a value that matched a known beacon from a test environment decommissioned six months ago.
Then she saw it. The Svalbard station’s ingest server had a silent RAM error—a single bit flip in a memory module used by the post-processing script. When the script ran 14 minutes after the transfer, it corrupted the file on disk. But here was the kicker: the corrupted file’s hash accidentally matched an old test signature Tripwire still had in its baseline.
Marta’s heart raced. She pulled up the FileCatalyst transfer logs. The file had arrived on time. But Tripwire showed that 14 minutes after FileCatalyst reported a successful checksum, the file had mysteriously been overwritten.
Marta was the lead security engineer for Arctic Helix , a joint polar research initiative. Every six hours, a 200GB seismic dataset from a remote ice station in Svalbard needed to be shipped to a supercomputer in Oslo. They used for this—it was the only thing that could push data that heavy across a shaky satellite link without failing.